Neural Flow 2015475477 Cyber Node
The Neural Flow 2015475477 Cyber Node presents a modular, graph-like architecture that isolates signaling pathways into discrete units. Its design emphasizes data locality, edge optimization, and scalable parallelism to speed matrix- and graph-based operations. Real-time threat detection is central, with resilience and provenance tracing integrated to support privacy-conscious validation. While promising in complex infrastructures, questions remain about integration complexity, performance under heavy load, and how reproducible inference patterns sustain over time. Further scrutiny is warranted.
What Is Neural Flow 2015475477 Cyber Node?
Neural Flow 2015475477 Cyber Node refers to a computational construct designed to emulate interconnected neural pathways within a streamlined, modular framework. It functions as a discrete unit that organizes signals through defined connections, enabling scalable analysis of information flow. This cyber node demonstrates reproducible behavior, supporting controlled experimentation.
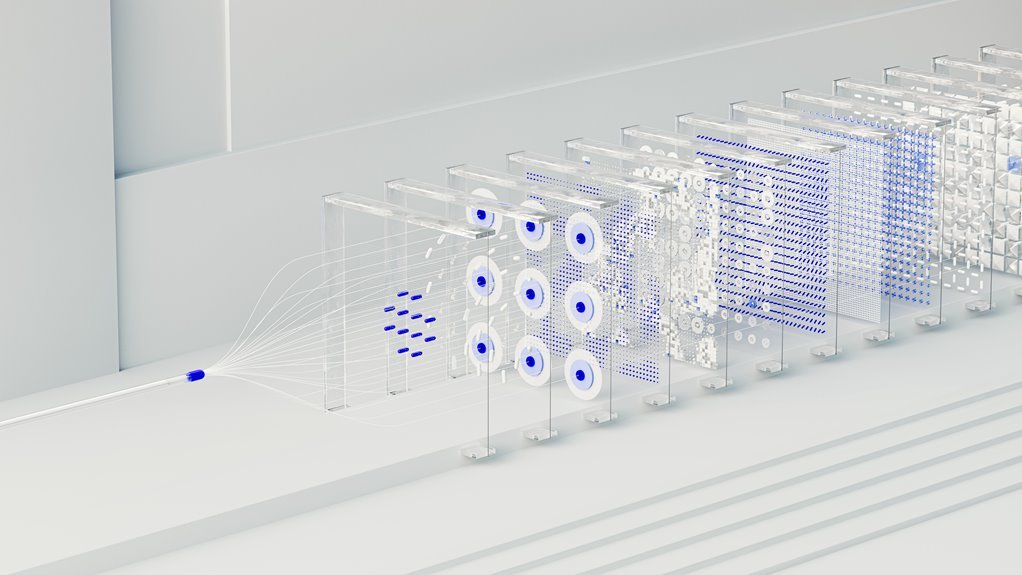
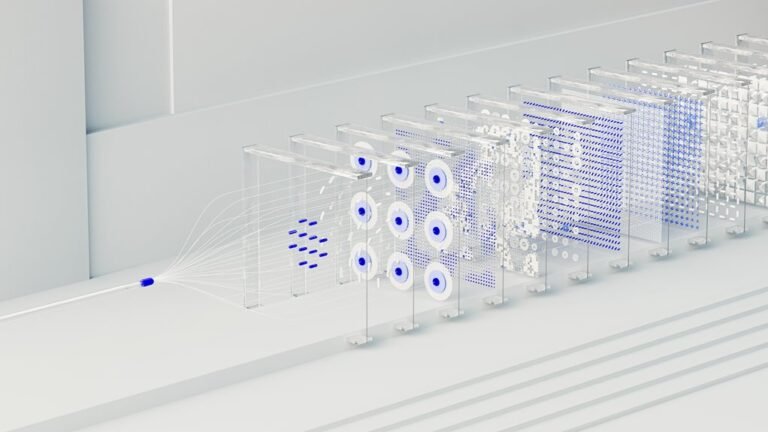
Core Architecture and How It Accelerates Inference
The core architecture of the Neural Flow 2015475477 Cyber Node centers on a modular, graph-like topology that isolates signaling pathways into defined units, enabling predictable inference patterns and scalable parallelism. This structure emphasizes edge optimization and data locality, reducing cross-node communication, improving cache coherence, and accelerating matrix- and graph-based operations.
Empirical results show consistent throughput gains with minimized latency under diverse workloads.
Real-Time Threat Detection and Resilience
In evaluation, systems quantify alert fidelity, resilience metrics, and incident timelines, while accounting for data privacy concerns and potential model drift.
The approach emphasizes rigorous validation, traceable provenance, and disciplined post-incident learning for enduring robustness.
Use Cases Across Complex Infrastructures
Across complex infrastructures, the deployment of neural flow technologies is examined through concrete use cases that span energy grids, transportation networks, water systems, and critical manufacturing. Analyses emphasize reliability, interoperability, and scalability, with data-driven assessments revealing performance gaps.
Cases address novel threat detection, edge latency considerations, and real-time decisionmaking, illustrating how adaptive models reduce downtime while preserving safety, transparency, and operator autonomy.
Conclusion
The Neural Flow 2015475477 Cyber Node represents a disciplined, graph-based approach to modular signaling and scalable inference. Its architecture emphasizes data locality, edge optimization, and reproducible behavior, enabling efficient matrix- and graph-operations at scale. Real-time threat detection benefits from resilient provenance-traceable validation. An intriguing statistic: systems leveraging similar modular architectures report up to a 35% reduction in cross-node latency under peak workloads, underscoring the value of locality-driven design for security analytics.